Left to Right: Panelists Mike Reiter, Lorrie Cranor, Ravi Sandhu and Carl Gunter (SACMAT 2010)

CyLab's Lorrie Cranor, Virgil Gligor & Lujo Bauer Contribute Support & Share Insights on Access Control at SACMAT 2010
by Richard Power
Trusted Infrastructure Workshop (TIW) 2010 wasn't the only important research-oriented event that Carnegie Mellon CyLab was integrally involved in last week, it was also making a significant contribution to the 15th Association for Computing Machinery (ACM) Symposium on Access Control Models and Technologies (SACMAT 2010), being held downtown at the Marriott Renaissance Hotel.
Carnegie Mellon CyLab joined with Mobility, Data Mining and Privacy (MODAP), a project funded by the European Union (EU), and University of Pittsburgh Laboratory for Education and Research on Security Assured Information Systems (LERSAIS) to provide invaluable support for the ACM Special Interest Group on Security, Audit and Control (SIGSAC) sponsored event.
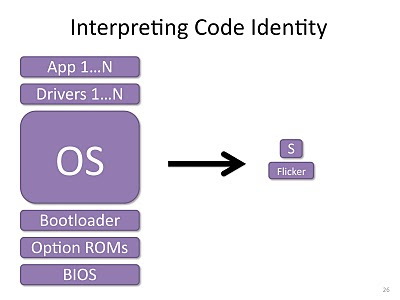
In addition to this organizational support, three CyLab team members participated in the SACTMAT program: CyLab Director Virgil Gligor delivered one of the keynotes, "Architectures for Practical Security," Lorrie Cranor, Director of the CyLab Usable Privacy and Security Lab (CUPS) joined in a panel on "Solving the Access-Control Puzzle: Finding the Pieces and Putting Them Together," and CyLab research faculty member Lujo Bauer served as one of the chairs for SACMAT 2010, and as a panel moderator.
CyLab Director Virgil Gligor keynoting at SACMAT 2010
SACMAT 2010 features presentations and discussions on issues and trends in Access Control, from "Towards Analyzing Complex Operating System Access Control Configurations" (Purdue University) to "Stateminer: An Efficient Similarity-Based Approach for Optimal Mining of Role Hierarchy" (University of Pittsburgh), and from "A Card Requirements Language Enabling Privacy-Preserving Access Control" (IBM Research Zurich) to An Access Control Model for Mobile Physical Objects (SAP Research).
In the panel on "Solving the Access-Control Puzzle: Finding the Pieces and Putting Them Together, Dr. Cranor shared her views with three other experts, Carl Gunter, University of Illinois at Urbana Champlain, Mike Reiter, University of North Carolina at Chapel Hill and Ravi Sandhu, University of Texas at San Antonio.
The panel's two moderators, CyLab's Lujo Bauer and Adam J. Lee, University of Pittsburgh, articulated three intriguing questions for the panelists to answer:
1. "What are some new or currently emerging topics that show a lot of promise to shape either practice or research, or both, over the next five to ten years?"
2. "What are a couple of areas that would benefit from interaction, that have typically been studied separately, i.e., pair x and y within Access Control and come up with something greater than the sum of its parts?"
3. "What is something that is getting tired? What have we explored to death."
Here are a few brief excerpts from the panelists' responses:
Mike Reiter: "What I think needs to be done in this field is to provide some way in which the system can assist the user, by leveraging evidence in the system to guide policy management. It shocks me that in all the time we have been working on access control, the process that the average user faces is still remarkably manual."
Ravi Sandhu: "To the first question: in one word, we need more automation ...We need to pay much more attention to automation than we are doing ... Things that have been sufficiently mined, and should be set aside: there was no shortage of things to put up here, but I thought it would be provocative to say SE Linux, on which I believe the US government has wasted a tremendous amount of taxpayer money, and they should stop doing it!"
Carl Gunther: "We have a number of access control models that people are very happy with, that they have done a lot of work with, and that have been shown to have some widespread applicability ... ABAC, RBAC, DTM. Yet, there is another level of work that has fallen short, and that requires more attention, a level that is different from what these models address, I will call it broadly 'process support for identity access management."
Lorrie Cranor: "A research area that requires more attention? Well, I would say that is access control with usability. A research area that has been sufficiently mined, and can be set aside? I would say that would be pretty much anything involving access control without usability. And two research areas that should be studied jointly? Well, pretty much anything you want as long as it is combined with usability."
CyLab's Lujo Bauer, one of the chairs of SACMAT 2010