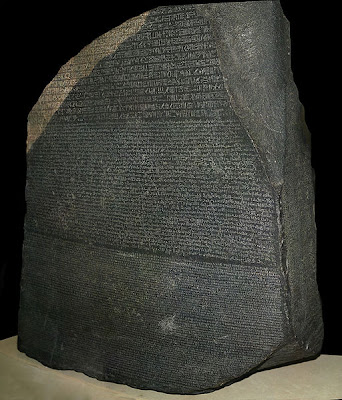
The Rosetta Stone Photo Credit: Hans Hillewaert CC-SA-BY-3.0 (Theme of RSA 2010)
When e-mail was just starting to be introduced in the workplace, I was a summer intern at IBM, before I went to graduate school, and you couldn't send anything outside of IBM, and there was a lot of struggle about whether or not to allow it. Now we are just seeing the exact same thing is repeating. -- Avi Rubin
People have been looking at social networks and crowds and how they reinforce productivity ... People who are on social networks are more productive, make better decisions, and have many advantages over those who are not. -- Kimberly De Vries
RSA 2010: Lifestyle Hacking -- Social Networks & Gen Y Meet Security & Privacy
By Richard Power
After a long morning of heavy hype and lofty notions at the RSA 2010 keynote sessions (see www.twitter.com/cylab for my 33 tweets from inside), I went looking for something to sink my teeth into. And therefore, not surprisingly, I drifted toward "Social Networks & Gen Y Meet Security & Privacy," a panel organized by the worthy IEEE Security and Privacy.
The panel was moderated by Gary McGraw, CTO, Cigital, and included Kimberly De Vries, Assistant Professor, CSU Stanislau, Avi Ruben, Professor, John Hopkins University, James Routh, Consultant, Archer Technologies and Gillian Hayes, UC Irvine.
Whatever Gary has his hand in is going to be refreshing, yet relevant, timely and yet ahead of the curve. This session was no exception.
He led off by having his panelists role-play in two little skits, both entitled "Pursuit of Productivity."
The first skit depicted a meeting between an H.R. Director, a CISO and a Chief Operating Office.
The COO remarked that there seemed to be some sort of generational gap, but that there was no way the enterprise could allow employees to fritter away time on social networking, declaring, "we need to focus on productivity."
The CISO showed the COO an analysis of recent security incidents, showing that they had increased dramatically, and that most were from the inside, because employees were seeking to by-pass the enterprise's controls to use social networking sites.
The COO responded, "Well, just tell me their names and we will fire them."
The HR Director then showed the COO results of studies that showed loosing up policy might make people more productivity, as well as the results of focus groups that showed in order to attract and hold on to the best candidates we have to update our current policy.
The COO remarked, "I never thought I would see the day when the security geek would propose loosening up policy, I will have to think about this ..."
In the second skit, the HR Director was depicted in a meeting with two employees who were both really outspoken about the need to access social networking, one from Sales and one from Technology.
The Sales person said, "I have over 600 contacts on LinkedIn."
The Technology person said, "On the product development team, if you don't keep up forget it, social networking is how I keep in touch with my peers and gurus."
The Sales person said, "I cannot be productive unless I clear my head with tunes on You Tube."
The H.R. Director asked for a percent of how much social networking was business as opposed to purely social.
The Sales person said, "It is very hard to compartmentalize between social and business."
The H.R. Director insisted, "I will need a percent for the form."
The Technology person answered, "LnkedIn: 100% business, 30% social."
The Sales person said, "Here's a percent, if LinkedIn and Facebook are banned, it is 100% certain I am going to quit; well, let's say 90%, yes, I have 600 contacts, and there's a 90% that one of them will hire me."
These two little skits really do capture the essence of a great upheaval going on inside the enterprise, in regard to how best to tap into the power of social media, without it turning into a well of woe.
Here are some of the insightful commentary from the panel discussion that followed.
Gary McGraw: Do controls encourage breaking rules? Is hacking around controls a gateway drug?
James Routh: It is not a gateway drug; it is more of a manifestation of a convenience factor. The generation that is coming out of school, and into corporate America, there are certain expectations coming to work, so to them, hacking around policy is trivial, it is not like crossing the line in their minds.
Gary McGraw: How do you define productivity? How do you balance maximum productivity against tools that do genuinely cause productivity loss?
Gillian Hayes: I am doing a lot of work with public schools, and what we see is this emphasis on 21st Century skills; what that means is solving problems creatively, and often that involves using technology, and it involves a sort of mash-up culture that kids have, i.e., grabbing bits and pieces of information, grabbing different services, bringing this all together, using your social network, etc. This is explicitly how we are teaching kids to solve problems when they are in school. It is probably a really good way to teach kids to solve problems, but we then put them into a very different environment. We take all those tools away, and say work inside this little sandbox. This is not a generation of people that is prepared for that. At the same time, what we are teaching them about information is "keep all your data private all the time." This is the abstinence-only model of teaching kids about security and privacy. So we have a real tension in which we are not teaching kids to make these decisions intelligently. Kids are taught very early: "Hide all the crazy things you're doing, but do them so that you can solve the problem."
Gary McGraw: Is there a parallel to the history of phones in the workplace?
Kimberly De Vries:Actually, there is a parallel to almost every new technology. Even if you go back and look at the introduction of writing, it was felt that if people learned to write, their memories would suffer, they wouldn't be able to focus. Plato complained about. People use to memorize everything, they use to be able to listen, people could remember; but if you can write things down and have that crutch, your brain is going to turn to oatmeal.
Avi Rubin: I have three elementary aged school children. I look at social networking and all the cool things you can do on-line, and say, "How cool is that, I can google this, and my GPS can tell me where I am ..." But my kids know no other world. If we go somewhere my son will tell me to pause the TV because he has to go to the bathroom. And I have to tell him, "we can't pause this TV, it's not one of those TVs." They use this stuff all the time. They live it, they breathe it. My son was using some video game that they play on-line, he knows how to get there, I don't ... He's seven years old. he created a user account. I overheard the conversation between my eleven year old and my seven year old. "Well, I need a user account and a password." And my daughter says, "Wel, don't use the same password that you use for other things, like your e-mail." "Well, how am I going to remember it?" "Here's what I do, have a good password, and then find something from that site and then combine it together, and if you go to another site, do the same thing with something from that site ..." I can't believe I a hearing my kids talk like this, they live in a completely different world.
Yes, I have been doing a lot of thinking, writing and speaking about the state of security and privacy, and where we are going in the future. And I have come to the conviction that the very nature of security and privacy must change radically to prevail, and that our best hope for this is the next generation, and the generation just beyond them. It was good to hear a similar sentiment echoed in the remarks of the panelists, particularly Hayes and Rubin.
