The single most important trend will continue to be exposing just how deeply the bad guys -- both cyber criminals motivated by financial gain, as well as nation states -- have penetrated nearly every aspect of our economy, government and private industry.
The single most important trend will continue to be exposing just how deeply the bad guys -- both cyber criminals motivated by financial gain, as well as nation states -- have penetrated nearly every aspect of our economy, government and private industry. Brian Krebs, Washington Post
It seems that today, while there is a lot of data on security, the data that matters is far harder to uncover. Robert Lemos, SecurityFocus
Vendors try to push their compliance, encryption and data loss prevention products on this notion that brand reputation is irreparably harmed in a breach, but it just ain't so. Michael Mimoso, Information Security Magazine
A very good journalist once said to me that often, the most important decision a reporter can make is *not* to write a story. It's hard in this beat. Bob Sullivan, MSNBC
CyLab Virtual Roundtable on Cyber Security News Media
-- Richard PowerThe professional challenges of cyber security are daunting. The problems confronted are extremely complex. The stakes are very high. You often find yourself the bearer of bad news, surrounded by
Pollyannas and
Chicken Littles. The priorities you are handed are often skewed. The motivations you encounter are often mixed. The resources you are allocated are usually inadequate. The executive mandates issued are typically tepid. Technological advancements race at light speed; meanwhile, organizational reforms crawl around in circles, at a snail's pace.
The professional challenges of cyber security journalism are almost as daunting. You must report on stories that, in large part, cannot be told, drawing on people who, in large part, cannot be quoted, and referencing statistics that are, in large part, suspect. All the while, you must separate hard news from hyperbole and be certain you are not the unwitting agent of some hidden agenda. And in the end, you must deliver a product that is comprehensible, informative, engaging and succinct to a public that is both skeptical and naive, distracted and over-stimulated.
Having experienced both sets of challenges first-hand, I have a great empathy and respect for those who endeavor to overcome them.
So here and now, in 2009, as we prepare (incredibly) to close out the first decade of the 21st Century, I felt it would be insightful and thought-provoking to check in with some of the best journalists covering the cyber security beat.
This virtual roundtable includes four friends and colleagues of mine, two from mainstream news media, two from cyber security industry news media, sharing their perspectives in response to four important questions.
The Washington Post's
Brian Krebs has an excellent blog,
Security Fix.
MSNBC's
Bob Sullivan also has an excellent blog,
Red Tape Chronicles.
Michael Mimoso is Editor in Chief for leading industry publication,
Information Security Magazine (aka SecuritySearch.com online)Robert Lemos is a freelance technology journalist and acts as the managing editor for Symantec's great site,
SecurityFocus.
Enjoy.
What is the greatest journalistic challenge in covering cyber security? What element of the subject matter makes the assignment most difficult?Brian Krebs, Washington Post: Probably the greatest challenge is getting people to care, and learn enough so that they can be a catalyst for helping others understand how important this issue is. The subject matter itself makes the assignment difficult: Explaining the latest threats simply and offering easy solutions without overburdening readers is a huge challenge, and one that becomes even more daunting every day. Here we have a communications medium that has become so central to everyone's lives, yet so few people have a grasp even the basics of how it works, or how they could live without it, until...well, for one reason or another usually related to insecurity, they are forced to live without it, however temporarily. The challenge is to grab the reader at those teachable moments, and use those to turn people into converts who place security on par with checking the sports scores, or all of the rest of the issues normal people care about on a day-to-day basis. That may sound unrealistic, but consider that the world we live in is only becoming more networked and linked together every day. What's more, very few readers have a sense of how a failure to stay educated about this medium contributes to the problem globally. A person whose PC or Web site is being used to blast out spam or host phishing Web sites, for example, is unlikely to ever be negatively affected by that experience. In addition, there are larger public policy and public safety issues stemming from computer and Internet insecurity that rise to the level of nation state concerns. These concerns also usually trace back to apathy, a lack of awareness, or a failure to act at an individual level.
Robert Lemos, SecurityFocus: For many journalists, the technical nature of cyber security can be a significant problem. Yet, for the most part, my readership comes from the security world, so the technical aspects of the beat are not as great a barrier. The real problem with cybersecurity is that there is a paucity of good data about security problems. Part of the issue is that companies do not want to talk about attacks or about their systems' weaknesses.
While such reticence may have been understandable in the past, times have changed. Fueled by easy -- albeit, unauthorized -- access to sensitive systems, espionage is undergoing a revival. Corporate computer systems are regularly being compromised by targeted attacks.
The networks of government agencies are being infiltrated by -- if not state-sponsored, then state-condoned -- hackers.
This is not just a journalism issue; it's a general security issue. A major government contractor had serious issues with the Conficker worm, but they would not talk about it on the record. When you can't understand the scope of a problem, it's difficult to combat the problem.
Michael Mimoso, Information Security Magazine: Off the top, you would think it would be the unwillingness of sources, especially in corporate and government settings, to speak to journalists about incidents, technology choices, best practices or anything else they believe might expose them to attack. And that's clearly understandable.
But I think the biggest challenge is that the majority of journalists are just that, journalists. Many of us don't have the technical background that our audience has, and yet our job, our mission, is to inform an audience that is closer to the subject matter than we will ever be. No matter what amount of homework I do on my own and how many security researchers I know and trust for information, my readers know the material better than I do and if I miss with an article, I'm going to get called on it. Ultimately, that makes me a better journalist, and forces me to be very careful and cynical of vendor FUD and hype.
Overall, I think the security media does a solid job, but a lot of our good work gets undone by the mainstream media. The mainstream media isn't as discriminating with its coverage-just look at Conficker and, for example, what 60 Minutes did with its piece-and ultimately, I think we're all painted with the same brush, which does a disservice to both our audiences.
Bob Sullivan, MSNBC: #1. The 'spook' factor, or the junior g-man factor. No one, it seems, ever wants to put their name on anything. So the stories are all reduced to "I know a guy who knows a guy who..says the Internet almost melted down last week." As a journalist I hate those stories. Combine that with the national security issue, and boy it's difficult.
#2. It's so easy to plant a scary story in some media outlet somewhere, which leads many editors to run into their newsrooms and say, "Why don't we have this story?" Similarly, it's easy to get front-page treatment when you write about a potential disaster, but hard when you write an even-handed story suggesting this or that might be overblown. A very good journalist once said to me that often, the most important decision a reporter can make is *not* to write a story. It's hard in this beat.
How has the cyber security beat changed over the years? How is it different now than it was five or ten years ago?Krebs: Cyber security as a concern is far more "in-your-face" that it ever was. Today, it is possible for people to find their Web browser, Facebook or Twitter account or whatever they use to interact online, hijacked by cyber thieves just by clicking on a link.
This type of activity is only the most visible symptom of a much larger problem, which is that hackers are now entirely motivated by financial gain, combined with very little chance of getting caught. They are organized, they reinvest their gains to make future attacks and scams more believeable, robust, and scalable, and they are more brazen and successful than ever.
Lemos: It's a cliche when talking about "The Old Days" -- which in Internet time is the early 90s, of course -- but they were a lot simpler. Journalists had better access to hackers and even the criminals who were circumventing computer security for fun and profit. Hackers and academic security researchers use to be open about what they were doing, and even when they weren't, techniques for hiding data were seldom used, so an enterprising reporter could learn more.
When at ZDNet in the late 1990s, I worked with other reporters there to analyze telltale information in the Melissa virus to help find out more about the author. With worms and attacks that followed -- from ILoveYou to Code Red to the MSBlast worm -- data became scarcer and scarcer. With MSBlast, Microsoft let slip that they had cleaned more than 8 million instances of the worm from systems, an unprecedented number. After it reached 25 million, the company stopped talking about the data. With the Conficker worm, there seems to be a lot less discussion about how widely it has spread. It seems that today, while there is a lot of data on security, the data that matters is far harder to uncover.
Mimoso: The story is much different. Two things have changed from 2000 when I started covering security: regulation and cybercrime. Security professionals in many instances have become compliance professionals. Investments in technology are often made based on a regulation an organization has to comply with. Policy decisions are often made based on a regulation an organization has to comply with.
That often leaves organizations with misguided priorities and a false sense of security. Cybercrime, meanwhile, is getting more pervasive and dangerous. It's the quiet attacks that should worry companies and individuals, more so than the splashy TJX-style data breaches. Hackers are using stealthy web-based malware to steal money from bank accounts, or intellectual property from large organizations. They're also conducting sophisticated denial-of-service attacks using botnets comprised of tens of thousands of compromised machines, in order to extort companies for large sums of money. All of this is incredibly troubling, profitable for the criminal and not going away any time soon.
Sullivan: Certainly, the spotlight has faded. Ten years ago, DefCon was actually interesting to a national audience. The Melissa virus really did impact everyone. Paradoxically, today's threats are more serious, involve much more money, etc., and yet they no longer capture the national audience quite as readily as they once did. That's not to say they don't capture attention at all -- certainly a big ID theft case, or a big virus, still nets big attention. But think about this: how many credit card have to be stolen for something to be a big story nowadays? The initial ChoicePoint story involved fewer than 100,00 records, and made front pages all around the country. Today, no one would even cover that story.
What is the most pervasive false meme that you confront among your editors and readers? What is the biggest blind-spot out there? Krebs: The idea that information security is something that is somehow beyond the capability or understanding of the average Internet user is a false meme that I encounter quite often. The reality is that it isn't realistic to expect people to protect themsleves from 100 percent of the threats 100 percent of the time, nor would you want people to live that way. That said, being safe online, being smart about your identity, avoiding scams and generally not being sucked into contributing to activities that scam or attack others, requires very few, relatively simple steps, mixed with a little bit of common sense.
Lemos: SecurityFocus readers are pretty savvy people, so this is less of a problem for me than most reporters. In the general populace, I see a lack of understanding of the insecurity of people's data and identity. We are still worried about breaches that release Social Security numbers, for example. In reality, we should assume that everyone's Social Security number has already been released and develop systems that do not rely on that piece of information as a key to our credit reports and financial data. Also, it still seems that people believe that somehow -- through security software and patching -- the threat of having your computer system compromised can be mitigated. It can only be reduced. Microsoft and others have documented that cybercriminals are focused on fooling users, not using technical exploits, to compromise computer systems. The biggest vulnerability on most computer systems is the user, and attackers have recognized that.
Mimoso: Data breaches hurting brand reputation. It's just not true. I think you'd be hard-pressed to find a company-aside from CardSystems which was ultimately forced to go dark before its assets were acquired-that was negatively impacted by a data breach. TJX is a good example. It is still cruising along; yes there was an initial hit to the stock price once news of the breach hit, but as of last summer, shares were selling higher than at any point since 2004. Vendors try to push their compliance, encryption and data loss prevention products on this notion that brand reputation is irreparably harmed in a breach, but it just ain't so. Same goes for data breach disclosure laws; while these laws have increased awareness around the importance of protecting data and identity theft, they have done little to make processes or systems more secure. And they do very little to influence customer behavior, especially with credit card breaches where very little liability is passed to the consumer.
Sullivan: I think it's really hard to steer both editors and readers towards the things that are really important, but perhaps more subtle. Every week there's a new study out that shows viruses are up, or vulnerabilities are up, or hacking attempts are up, and these make for great headlines. But the studies are often poorly designed and don't mean much. On the other hand, for example, I really want people to think twice before they sign up for supermarket loyalty cards and EZ-Pass and those kinds of invasive technologies. I at least want them to understand the consequences before they do it. How do I make that story sexy enough to compete with a story about an alleged Internet meltdown that's coming? There's no easy answer.
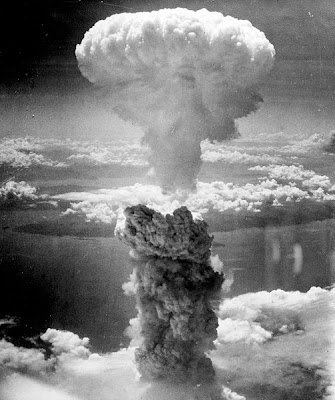
From your perspective as a journalist, what issues and trends jump out at you as particularly important or dominant in the coming year?Krebs: A major contributor to the success of these gangs is that the most powerful nation on Earth still can do very little to touch cyber criminals operating in certain countries. The single most important trend will continue to be exposing just how deeply the bad guys -- both cyber criminals motivated by financial gain, as well as nation states -- have penetrated nearly every aspect of our economy, government and private industry. Longer term, if this situation does not change, if we cannot succeed in bringing cyber gangs to jutice, we will have missed an important opportunity. I believe that five or ten years from now, we may well look back fondly on the age we live in now as a time when we still had an opportunity to kill some of this cyber crime in the crib and disperse the organizations that are driving it. I believe our inability to apprehend and bring to justice those who are responsible for stealing hundreds of millions of dollars from consumers and businesses is going to haunt us down the road, as these groups mature, become more emboldened, and more entrenched in the political and economic classes of the countries that act as safe havens for them.
Lemos: The most important trend is that, in the midst of a boom in cybercrime and cyber espionage, the United States and other nations have started formulating better defensive strategies and a doctrine for offensive actions in cyberspace. Whether these nations create a good policy or create policies that attempt to control the Internet for no real gain, will be a significant story over the next few years.
Mimoso: The economy. It's going to be interesting to see how the recession impacts the emphasis companies place on information security. For instance, are important security projects/investments going to be tabled or canceled altogether? A lot of companies are paying lip service right now to the importance of keeping data and customer information secure and maintaining the integrity of security programs during this downturn. But security is traditionally a cost center where ROI is extremely difficult to prove. We'll see if the bottom line ultimately wins out. An offshoot of the recession too is whether we'll see additional regulation coming out of this. Chances are we will, but it will likely take some time before we see any real impact.
Sullivan: 1. Attackers targeting Facebook and other social networking tools.
2. Cyber cold war: Real now?
3. Impact of the economic downturn on security. Companies cutting back? Layoff revenge? Consumers taking more risks?