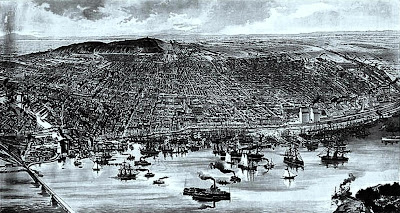
The city proper covers most of the of the Island of Montreal at the confluence of the Saint Lawrence and Ottawa Rivers. The port of Montreal lies at one end of the Saint Lawrence Seaway, which is the river gateway that stretches from the Great Lakes into the Atlantic Ocean.[36] Montreal is defined by its location in between the St. Lawrence river on its south, and by the Rivière des Prairies on its north. The city is named after the most prominent geographical feature on the island, a three-head hill called Mount Royal, topped at 232 m above sea level. Wikipedia
Android Security, Naked Keystrokes, Selling Viagra, Crying Wolf & More! -- A Report from the 18th USENIX Security Symposium (Montreal, 2009)
By Richard Power
The 18th USENIX Security Symposium was held in Montreal, Quebec (August 10-14, 2009). This conference always provides an excellent opportunity to catch up on the thinking of some impressive minds and delivers the most technical content of all the major security-focused IT conferences.
USENIX distinguishes itself by being a non-profit organization, and acting like one. Seventy-nine students were given stipends to attend this year’s Security Symposium, at a cost of approximately $100,000. This is how USENIX spent the contributions of its sponsors, as well as a significant chunk of its own funds. None of the commercial conferences can lay claim to any such altruism.
I asked legendary login editor Rik Farrow (well, he is the Editor, and kept up the publication’s high standards for many years, enough to qualify as a legend in this field, and yes, he is my friend) how he would distinguish USENIX Security Symposium from the other major cyber security conferences?
“USENIX Sec is one of four top tier security research conferences, and certainly my favorite because accepted papers must include an implementation. So this goes well beyond theory.”
Rich Cannings, Android Security Leader at Google delivered the keynote, “Securing a Mobile Platform from the Ground Up.”
Here are my notes from the talk --
Cannings started off by breaking down the numbers:
-- 6.77 billion human beings on the planet.
-- 1.48 billion Internet-enabled PCs
-- 4.10 billion mobile phones, with a 12-18 month average replacement rate.
-- 1 billion mobile phone purchases per year
“And 13.5% of them are smart phones. This number will soon compare with the number of Internet enabled PCs, and they will become major security targets.”
Next, Cannings gave some background on Android:
Google’s Android is free, open source mobile program, intended to “empower both users and developers.”
It has a Linux kernel. It relies upon 90+ open source libraries (e.g., SQLite for structured data storage, OpenSSL, etc.). It supports common codes for sound, image, etc.
Android is also “designed to protect battery life.”
Developers don’t understand battery life
Users do.
In outlining Google’s security philosophy in regard to Android, Cannings articulated some of the premises with which they approach the issue:
-- Finite time and resources
-- Humans have difficulty understanding risk
-- Safer to assume that most developers do not understand security
-- Most users do not understand security
The cornerstones of the Android security philosophy, as formulated by Cannings, emphasize some basic needs:
-- Need to prevent security breaches from occurring
-- Need to detect them when they occur
-- Need to minimize their impact
-- Need to react to both to vulnerabilities and breaches swiftly
Cannings went on to explore each of these elements as they came into play in the development, roll-out and support of Android.
No one with serious experience in cyber security could argue with Cannings’ guiding principle: “Security is an ongoing process, not a checkbox.”
But of course, Android means “five millions lines of new code,” utilizing, as I mentioned earlier, one hundred open source libraries. And since Android is open source, Cannings remarked, it “can’t rely on obscurity.”
There are tremendous challenges ahead.
Farrow elaborates.
“I liked the keynote, as I am very concerned about the security of mobile devices. The obvious trend is for people to use their smart phones as their primary method for interacting with the Internet, and I would love to see the security of phone software fare MUCH better than Windows has in this area. Rich Canning did a good job of describing the Android security model, but I was left feeling that there are real weaknesses in the Android security model largely because the Android team is being rushed, and layering their security on top of ancient UNIX security features. The notion of relying on users to permit applications based on the number and importance of privileges required is flawed, as most people make poor security decisions (and there is lots of research to back this up).
“Android does present a chance to create a secure environment,” Farrow adds, “but it must also satisfy both developers and users if it is to be successful.”
The program committee received one hundred seventy submissions for this year’s Symposium, only twenty-six papers were accepted.
Martin Vuagnoux and Sylvain Pasini of LASEC/EPFL received an “Outstanding Paper” award for “Compromising Electromagnetic Emanations of Wired and Wireless Keyboards.” These students cobbled together a system capable of converting broad spectrum radio emissions of keyboards into actual keystrokes.
Roxana Geambasu, Tadayoshi Kohno, Amit A. Levy, and Henry M. Levy of University of Washington also received an “Outstanding Papers” awards for “Vanish: Increasing Data Privacy with Self-Destructing Data.”
Carnegie Mellon University was represented by Joshua Sunshine, who presented “Crying Wolf: An Empirical Study of SSL Warning Effectiveness,” headline-grabbing research conducted with Serge Egelman, Hazim Almuhimedi, and Neha Atri, under the guidance of Lorrie Cranor, Director of CyLab’s Usability of Privacy and Security Lab.
Of course, CyBlog covered this compelling research, recently, when the story broke. (See CyLab CUPS Researchers Release Study on SSL Warning Effectiveness)
CyLab corporate partners can read my full report on the 2009 USENIX Security Symposium, including my notes on Vern Paxson's “How the Pursuit of Truth Led Me to Selling Viagra” and interview with Metronics 4.0 chair, Jennifer Bayuk, in the Intelligence Briefing section of the CyLab partners-only portal.
